Asymmetric Warfare in the Iranian Conflict: A Technical Autopsy of Infrastructure Exposure
The Iranian conflict revealed with uncomfortable clarity how modern asymmetric warfare exploits the fragility of critical infrastructure, exposing the tightly coupled engineering systems that underpin global stability. Analysts have long warned that infrastructure behaves as a system‑of‑systems, where disturbances in one domain propagate rapidly into others—a reality emphasized in the U.S. Cybersecurity and Infrastructure Security Agency’s National Risk Profile, which notes that “cascading failures across sectors are increasingly likely due to digital and physical interdependencies.” During the conflict, this interdependence became visible as data centers, LNG facilities, pipeline networks, power grids, and maritime chokepoints all experienced targeted pressure designed not to destroy assets outright, but to degrade operational continuity. Data centers proved especially vulnerable due to their sensitivity to power quality, cooling stability, and fiber route concentration. Even minor voltage or frequency disturbances can trigger UPS transfers or generator engagement, a weakness highlighted in the Department of Energy’s grid modernization studies. High‑density compute racks, often running at 20–80 kW per rack, rely on uninterrupted chilled‑water or DX cooling, making rooftop cooling assets and pump VFDs attractive targets for low‑cost drones or cyber probing. Meanwhile, the European Union Agency for Cybersecurity has repeatedly documented that physical fiber cuts remain one of the most effective low‑cost disruption methods, underscoring how a single severed corridor can ripple across cloud and industrial workloads.
LNG facilities, with their high‑energy cryogenic processes and low tolerance for operational deviation, faced similar asymmetric pressure. Liquefaction trains depend on multi‑stage compression, precise refrigerant balance, and stable feed gas conditions; even small disturbances in compressor performance or feedstock quality can halt production, as noted by the U.S. Energy Information Administration. Submerged LNG pumps, operating within narrow NPSH and speed envelopes, are particularly sensitive to VFD anomalies or harmonic distortion. Upstream pipeline networks added another layer of fragility, with the Pipeline and Hazardous Materials Safety Administration reporting that pressure fluctuations or valve misoperations can propagate rapidly across long distances. These technical realities meant that even modest asymmetric actions—drone reconnaissance of tank farms, cyber probing of compressor PLCs, or maritime harassment delaying tanker berthing—produced global LNG price volatility and forced operators to confront how little margin for error exists in cryogenic energy systems.
““The cold boxes are gone… this is the main unit, that is the cooling box of the LNG — it is completely destroyed.””
The power grid, often described as the most complex machine ever built, demonstrated how deeply asymmetric tactics can stress a system designed for efficiency rather than resilience. Frequency stability remains a critical vulnerability, and the North American Electric Reliability Corporation has warned that malicious actors may exploit inverter‑based resource behavior during disturbances. Substation automation systems built on IEC 61850 protocols expand the cyber attack surface, while large power transformers—requiring 12–24 months to replace—represent single points of failure with limited domestic manufacturing capacity, as detailed in the Department of Energy’s transformer supply chain review. Low‑level cyber intrusions, physical attacks on remote substations, and drone interference with transmission corridors did not collapse the grid, but they forced operators to confront how easily distributed pressure can bend system stability and trigger protective relays across wide geographic areas.
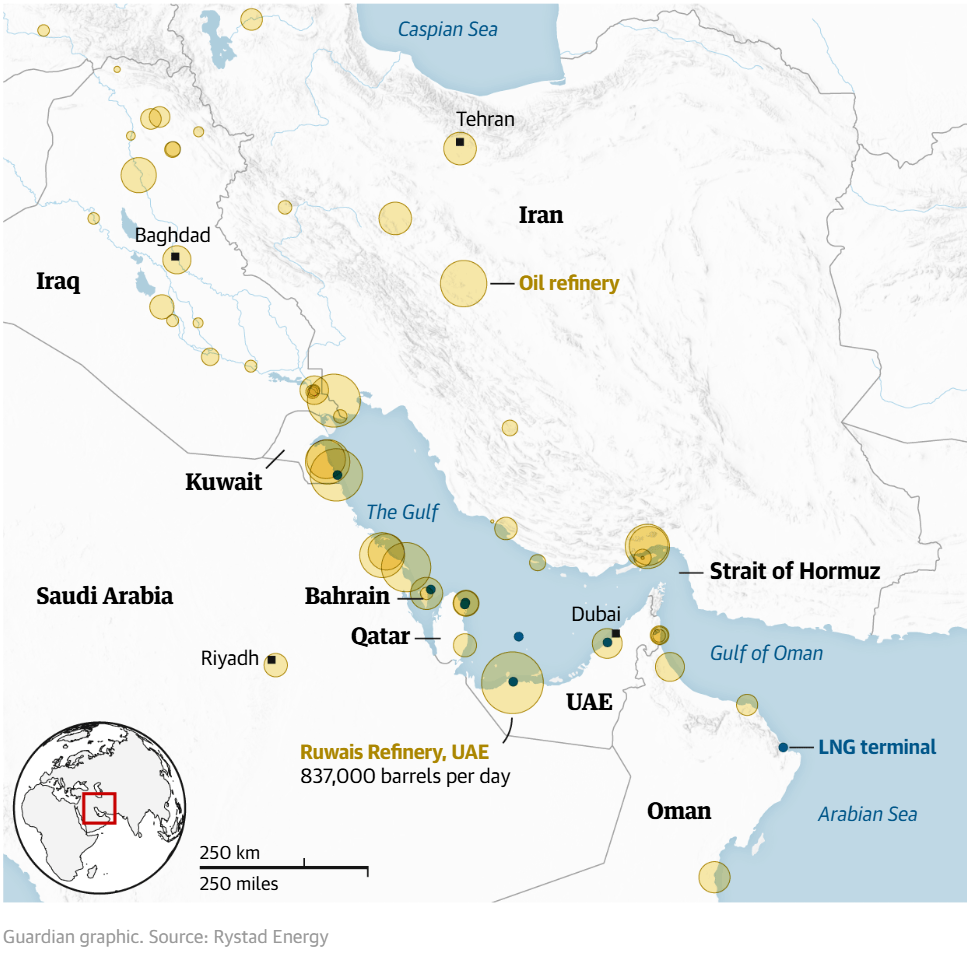
Maritime chokepoints added yet another dimension to the conflict’s asymmetric landscape. The International Maritime Organization has documented rising cases of AIS spoofing affecting tanker routing, and the Strait of Hormuz—through which 20–30% of global LNG and crude flows—proved that even temporary slowdowns can create global supply ripples. Port infrastructure, increasingly digitized and reliant on SCADA systems, faced cyber probing and operational delays that compounded upstream energy disruptions. The conflict demonstrated that maritime logistics, energy production, and digital infrastructure are no longer separate domains—they are interdependent layers of a single global operating system.
Across all these domains, the engineering lesson was unmistakable: traditional perimeter defense is obsolete. Infrastructure operators must shift toward preservation engineering—designing systems that degrade gracefully rather than fail catastrophically, incorporating autonomous isolation of compromised subsystems, deploying multi‑vector anomaly detection across thermal, electrical, cyber, and acoustic domains, and building distributed redundancy that reduces reliance on single corridors or single facilities. This aligns with the National Infrastructure Advisory Council’s conclusion that resilience must be engineered as a primary design parameter, not an afterthought. The Iranian conflict did not invent asymmetric warfare, but it demonstrated how deeply infrastructure has become the preferred battlefield. Data centers, LNG terminals, pipelines, grids, and ports are no longer background utilities; they are strategic terrain. And the engineers responsible for designing and operating them now sit at the front line of global stability.
References
CISA (2023). National Risk Profile. Cybersecurity and Infrastructure Security Agency.
DOE (2022). Grid Modernization and Power Quality Report. U.S. Department of Energy.
ENISA (2023). Threat Landscape Report. European Union Agency for Cybersecurity.
EIA (2023). LNG Operational Overview. U.S. Energy Information Administration.
PHMSA (2022). Pipeline Incident Annual Report. Pipeline and Hazardous Materials Safety Administration.
NERC (2023). Inverter-Based Resource Performance Report. North American Electric Reliability Corporation.
DOE (2022). Large Power Transformer Supply Chain Review. U.S. Department of Energy.
IMO (2023). Cyber Risk Management Guidelines. International Maritime Organization.
NIAC (2022). Infrastructure Resilience Framework. National Infrastructure Advisory Council.